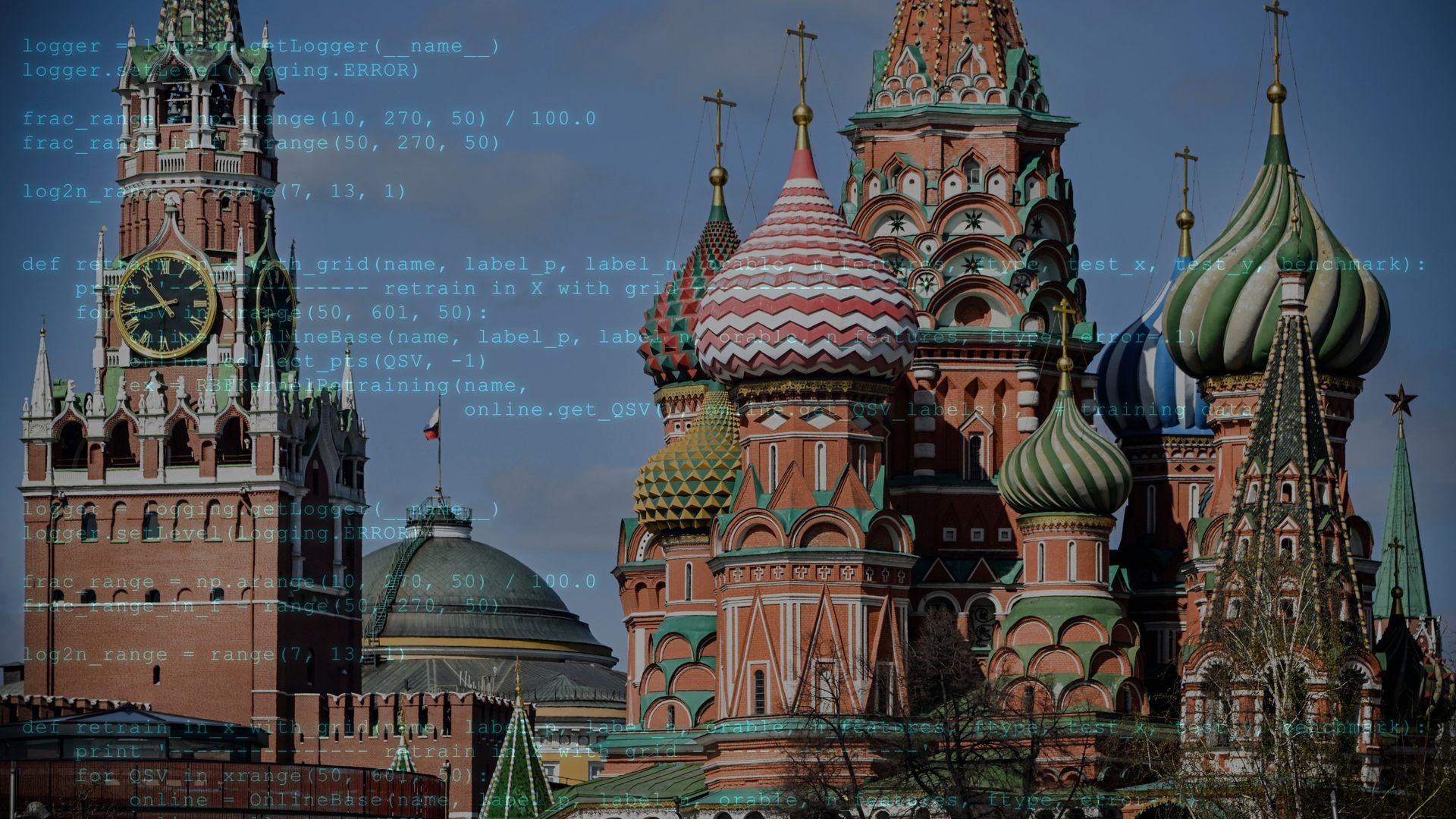
Russia forged new cyber weapons to attack Ukraine. Now they're going international
#Russia #cyber weapons #Ukraine #international #cyber attack #security threat #global expansion
📌 Key Takeaways
- Russia developed new cyber weapons initially targeting Ukraine.
- These cyber weapons are now being deployed internationally.
- The expansion indicates a broader cyber threat beyond the Ukraine conflict.
- The shift suggests Russia is testing or escalating its cyber capabilities globally.
📖 Full Retelling
🏷️ Themes
Cyber Warfare, International Security
Entity Intersection Graph
No entity connections available yet for this article.
Deep Analysis
Why It Matters
This development matters because it signals an escalation in global cyber warfare, moving from targeted attacks on Ukraine to broader international threats. It affects governments, critical infrastructure operators, and private corporations worldwide who must now defend against sophisticated Russian cyber weapons. The internationalization of these tools increases risks of economic disruption, espionage, and potential retaliation between nations, potentially destabilizing global digital security. Ordinary citizens also face increased risks of data breaches, service disruptions, and collateral damage from cyber conflicts spilling into civilian systems.
Context & Background
- Russia has conducted cyber operations against Ukraine since at least 2014, including the 2015 and 2016 power grid attacks that caused widespread blackouts
- The NotPetya malware attack in 2017, initially targeting Ukraine, spread globally causing over $10 billion in damages worldwide
- Russia's GRU military intelligence agency has been linked to numerous cyber operations including attacks on the 2016 US elections and the 2018 Winter Olympics
- Ukraine has developed into a 'cyber battlefield laboratory' where Russia tests new digital weapons before deploying them elsewhere
- The 2022 full-scale invasion of Ukraine was preceded by massive cyber attacks including wiper malware targeting government and financial systems
What Happens Next
NATO and allied nations will likely enhance cyber defense cooperation and intelligence sharing in response. Expect increased sanctions on Russian cyber entities and individuals by Western governments within 2-3 months. Cybersecurity firms will release detailed analyses of the new Russian tools within weeks, enabling better detection. There's high probability of retaliatory cyber operations from Ukraine's allies against Russian infrastructure. International organizations like the UN may attempt to establish new cyber warfare norms, though with limited success given current geopolitical tensions.
Frequently Asked Questions
Russia is developing advanced malware, wiper tools that destroy data, industrial control system attacks targeting critical infrastructure, and sophisticated phishing campaigns. These weapons have evolved through battlefield testing in Ukraine and now incorporate evasion techniques to bypass traditional security measures.
NATO members supporting Ukraine face the highest risk, particularly Eastern European nations like Poland and the Baltic states. Critical infrastructure operators in energy, finance, and transportation sectors globally are vulnerable. Nations imposing sanctions on Russia also face increased targeting of government and corporate networks.
Organizations should implement zero-trust security architectures, regularly patch systems, conduct employee cybersecurity training, and deploy advanced threat detection tools. Critical infrastructure operators need air-gapped backups and incident response plans. International information sharing through ISACs (Information Sharing and Analysis Centers) provides early warning of emerging threats.
Russia seeks to retaliate against nations supporting Ukraine, test weapons in diverse environments, gather intelligence on adversaries, and create economic pressure to reduce support for Ukraine. International attacks also serve as demonstrations of capability for geopolitical leverage and may distract from battlefield challenges in Ukraine.
The new weapons incorporate lessons from Ukraine conflict, making them more adaptive and evasive. They likely feature improved persistence mechanisms, faster propagation methods, and targeting capabilities for diverse international systems. Unlike earlier tools designed for specific Ukrainian infrastructure, these are engineered for broader compatibility with global networks.